The developers of Mofo Linux talk a good game. From the name’s origin in abusive street slang to its self-description on the home page as “Linux designed to defeat state censorship and surveillance,” Mofo presents itself as a champion of security and privacy. Nor is the claim unjustified. However, rather than putting security and privacy into the hands of ordinary users, Mofo simply presents the tools and leaves users to figure them out with a minimum of help. The result is a promising distribution that with only slightly more work, could be a leading one.
Just possibly, though, this approach is a deliberate tactic, and not the carelessness it appears. Based on Ubuntu, the current release of Mofo offers nothing different in the way of productivity tools. It uses Unity for a desktop, and its applications are the standard GNOME ones. In fact, Mofo shows such little interest in such matters that it does not bother to change the title bar in the installer from Ubuntu.
However, users logging in for the first time can hardly miss the line of unfamiliar applications on the dashboard. Below the search field at the top, instead of Firefox and LibreOffice, the dashboard displays a seven security applications, at least several of which are likely to be unknown to many users. As a result, users have no choice except to look up each application, one by one. The only help is a relatively brief introduction on the project home page, which only explains where to find each installed tool.
Assuming that users do not tire of the unexpected needed to educate themselves, by the time Mofo is ready to use, they will become instant experts in a way that clear and complete documentation might not allow. If so, the tactic is an ingenious one. However, it is still a nuisance for those who are more interested in immediate results — that is, I suspect, most downloaders of the distribution image.
There are simply too many unknowns, and not enough notifications of minor facts such as the fact that Firefox is set to run encrypted Google searches by defaults.
Flying in the dark
A prime example of what users face is the treatment of tools for web anonymity. Mofo includes two tools for this purpose, Tor Browser and I2P — and users can only infer that Tor is present by references to it on the project web site.
Unfortunately, what it does not include is any indication which one you should use in which circumstances. Can you simply choose one? Or, if you choose both, are there any dangers of conflicts?
Moreover, if you miss the introduction on the web, the only way that you will stumble across Freenet, which enables censorship-free peer to peer transfers is by accident. Yet, even if you do find the introduction, you find yourself abruptly dealing with an unexplained reference to cjdns, which installs an encrypted IPv6 meshed networking protocol for use in so-called darknets, and Hyperboria, a popular network that uses cjdns.
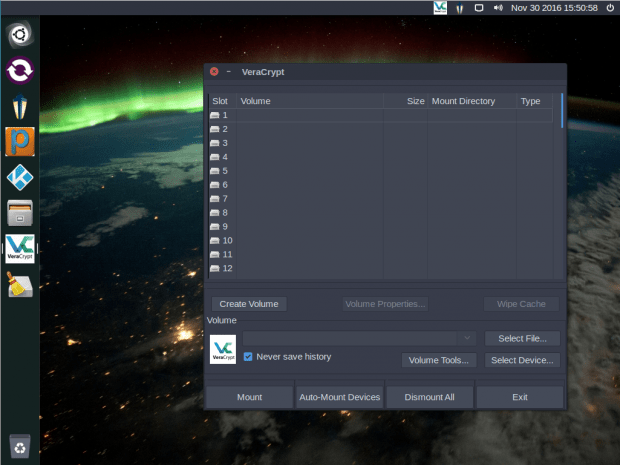
A similar situation exists with local encryption. VeraCrypt is on the dash, and is capable of encrypting entire systems or individual filesystems, placing them in containers, which it treats like files. It also allows the slick trick of hiding one of these files within another file, effectively hiding it from view.
Yet how does VeraCrypt compare with zuluCrypt and eCryptfs, which are also included and perform similar functions? Is the choice of which to use simple a matter of personal preference? Or would there be an advantage to mixing them, using different ones in different situations? The same questions also arise with Mofo’s half dozen VPM applications. Is the placement of Psiphon on the dashboard an implicit recommendation, or would other VPM tools be more useful in specific cases? At least the introduction gives brief but adequate instructions for setting up VPM.
Mercifully, though, other launchers on the dashboard are largely self-explanatory. Most users should only need to click on OnionShare to figure that it is a tool for encrypted file-sharing. The same is also true for Lantern, which is designed to evade efforts at state censorship, although as a courtesy users might be warned of possible consequences.
At least in the current release of Mofo, the video player’s BitTorrent client with its ability to infringe copyright is disabled, removing one source of unpleasant surprises for users. Still, that said, those who might want to use it regardless of risk are left on their own, making its inclusion pointless from any perspective.
By the time users get to BleachBit, a tool that cleans systems, thereby assisting security and privacy, it seems almost mundane and a model of clarity
Nor are the contents of the dashboard all the tools Mofo offers. For example, opening Thunderbird for the first time opens the installer for Engima Mail to enable encrypted emails. However, such tools must be discovered serendipitously.
Unfulfilled Potential
I want to like Mofo more than I do. With more and more users wanting security and privacy but being unsure where to begin, Mofo’s selection of tools could easily evolve into an important distribution.
However, to fulfill this potential, Mofo needs to pay serious attention to its documentation. As things are, even someone with reasonable knowledge of security and privacy will probably find configuring Mofo heavy going. In this respect, Mofo trails far behind other leading security-based distributions like Qubes OS and Subgraph that make far more thorough efforts to bring the benefits of the included tools to the average user.
Adding documentation would not only aid users, but also add credibility to the distribution. Securing a system is all about taking pains and weighing the risks. By contrast, the way that Mofo simply offers various useful tools — some of which have hidden dangers and problems — does not exactly inspire confidence in the distribution. After all, when you are trying to harden your installation and work flow, you do not expect to have unexpected consequences.
Still, Mofo is worth investigating — not for what it does, but what, with a little more effort, it could do.
[sharedaddy]